When the Software Update Became the Weapon
It began quietly.
No alarms. No crashing systems. No ransom notes.
In early 2020, thousands of organisations around the world installed what appeared to be a routine software update. It came from a trusted vendor, digitally signed and delivered through normal channels. For IT teams, it was just another maintenance task, update the software and move on.
But hidden inside that update was something else.
A carefully crafted piece of malware.
By the time investigators uncovered the truth in December 2020, the attackers had already infiltrated government departments, security companies, and major corporations across the world.
This was the SolarWinds supply chain attack, one of the most sophisticated cyber-espionage campaigns ever discovered.
And the most disturbing part?
The victims installed the backdoor themselves.
The Company at the Centre
SolarWinds develops network management tools used by thousands of organisations worldwide. One of its flagship products, Orion, allows IT teams to monitor servers, infrastructure, and network performance from a central console.
Because Orion integrates deeply into enterprise networks, it often has extensive visibility and privileges inside an organisation’s systems.
That level of trust made it a perfect target.
Government agencies, multinational companies, and security firms all relied on Orion to manage critical infrastructure.
If attackers could compromise SolarWinds itself, they could potentially reach all of those organisations at once.
A Patient Intruder
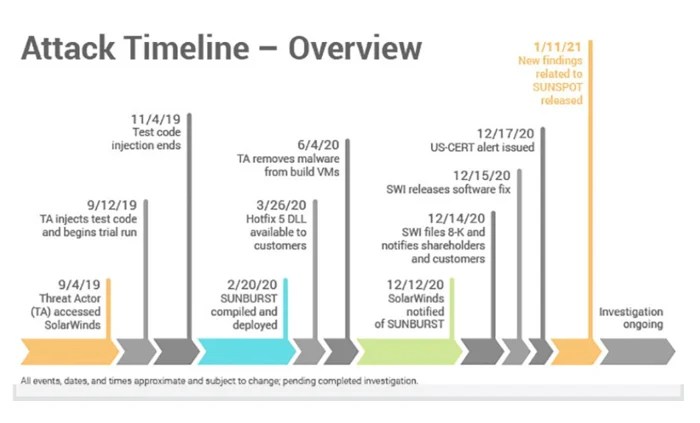
Investigators later discovered that attackers likely gained access to SolarWinds’ internal systems sometime in 2019.
They didn’t move quickly.
Instead, they studied the company’s software development pipeline — the systems used to build, compile, and distribute Orion updates.
Eventually, they managed to compromise the software build environment.
This meant that when SolarWinds engineers compiled the Orion software, malicious code could be silently inserted into the final product.
The attackers had effectively turned SolarWinds’ own development process into a delivery mechanism.
The Trojan Update
The malicious code embedded into the software was later named SUNBURST.
Between March and June 2020, SolarWinds unknowingly distributed infected Orion updates to customers around the world.
These updates appeared completely legitimate.
They were:
- digitally signed by SolarWinds
- downloaded through official update channels
- trusted by antivirus and security tools
Around 18,000 organisations installed the compromised update.
But the attackers were selective.
Only a small number of those networks were chosen for deeper exploitation.
A Backdoor That Whispered
SUNBURST was designed with extreme stealth.
After installation, the malware remained dormant for days or weeks before contacting attacker-controlled servers.
Its communications were disguised to look like legitimate SolarWinds traffic, helping it avoid detection by security systems.
Once activated, the attackers could:
- move laterally across networks
- steal credentials
- access sensitive data
- monitor communications
- maintain long-term persistence
In some cases, attackers remained inside victim networks for months without detection.
The Breach That Discovered Itself
Ironically, the breach wasn’t discovered by SolarWinds or its customers.
Instead, it was uncovered by the cybersecurity company FireEye.
In December 2020, FireEye noticed suspicious activity within its own internal systems. While investigating the breach, analysts traced the intrusion back to a compromised SolarWinds Orion update.
That discovery triggered a massive global investigation.
What researchers uncovered stunned the cybersecurity community.
A trusted software update had become a delivery system for a global espionage campaign.
Who Was Behind the Attack?
Although attribution in cyber operations is rarely absolute, investigators quickly began to identify patterns.
Security researchers and intelligence agencies linked the operation to a Russian state-sponsored threat group known as APT29, also commonly called Cozy Bear.
APT29 has long been associated with Russia’s foreign intelligence service, the SVR.
The group has previously been linked to several high-profile espionage campaigns, including attacks on diplomatic organisations and government networks.
Multiple governments, including the United States and the United Kingdom, publicly attributed the SolarWinds operation to Russian intelligence.
Unlike ransomware attacks driven by financial gain, the SolarWinds operation appeared to be strategic intelligence gathering.
The attackers focused on government departments, policy organisations, and technology companies that could provide valuable geopolitical insight.
The SolarWinds breach was a turning point for the cybersecurity industry.
Trust Was Weaponised
Security best practice normally encourages organisations to install updates quickly.
In this case, the update itself was the attack vector.
The Supply Chain Became the Target
Rather than hacking thousands of organisations individually, the attackers compromised a single trusted supplier and gained potential access to thousands of networks.
Extreme Sophistication
SUNBURST was carefully engineered to evade detection by:
- delaying execution
- mimicking legitimate traffic
- activating only under specific conditions
This level of stealth allowed the attackers to remain hidden for months.
Lessons From SolarWinds
The attack reinforced several key cybersecurity lessons.
Third-party risk is critical
Vendors and suppliers can become entry points into your network.
Secure the software supply chain
Development pipelines, build systems, and signing infrastructure are high-value targets.
Detection matters as much as prevention
Even strong security controls can be bypassed.
Adopt an assume-breach mindset
Modern security strategies increasingly focus on detecting attackers already inside the network.
Final Thoughts
The SolarWinds attack wasn’t loud.
There were no immediate system failures or obvious warning signs.
Instead, it was quiet, methodical, and deeply strategic.
By compromising a trusted software update, attackers turned a routine maintenance process into a global espionage platform.
The incident exposed a difficult truth about modern technology:
Our digital infrastructure is deeply interconnected, and when trust is exploited in one place, the impact can ripple across thousands of organisations worldwide.
SolarWinds wasn’t just another breach.
It was a warning.
Sources & Further Reading
National Cyber Security Centre (UK)
https://www.ncsc.gov.uk
CISA SolarWinds Advisory
https://www.cisa.gov/news-events/cybersecurity-advisories/aa20-352a
SolarWinds Investigation Blog
https://www.solarwinds.com/blog/new-findings-from-our-investigation-of-sunburst
Center for Internet Security Analysis
https://www.cisecurity.org
Fortinet SolarWinds Attack Overview
https://www.fortinet.com/resources/cyberglossary/solarwinds-cyber-attack
Leave a comment